The modern smartphone has evolved from a simple communication device into the central hub of daily life, managing everything from financial transactions to critical work communications. When an Android device encounters a system error, the disruption extends far beyond mere inconvenience; it can halt productivity and compromise data security. While many minor glitches resolve themselves with a restart, persistent system errors often require more robust intervention. This is where Personal Computer (PC) based repair tools become indispensable. Unlike on-device fixes that may be inaccessible when the operating system is compromised, PC tools offer a deeper level of access to the device’s firmware and partition structures. Understanding how to leverage these tools safely is essential for technicians and advanced users alike, ensuring that devices are restored to full functionality without risking permanent data loss or hardware damage.
Understanding the Nature of Android System Errors
Android system errors manifest in various forms, ranging from benign application crashes to catastrophic boot loops where the device cannot load the operating system. These issues often stem from corrupted system files, failed over-the-air (OTA) updates, incompatible custom modifications, or flash memory degradation. When the Android runtime environment detects critical failures in the kernel or system partition, it may trigger a “soft brick,” rendering the interface unresponsive while the hardware remains intact. In more severe cases, known as “hard bricks,” the device fails to power on or enter download mode entirely. Diagnosing the specific type of error is the first critical step in the repair process, as the solution varies significantly depending on whether the bootloader is accessible or if the device is stuck in a recovery loop.
The complexity of the Android ecosystem contributes to the frequency of these errors. With thousands of device models running different versions of the OS and customized user interfaces from manufacturers like Samsung, Xiaomi, and Google, a one-size-fits-all solution rarely exists. System partitions such as /system, /boot, and /recovery must remain intact for the device to function. Corruption in these areas often requires reflashing the stock firmware, a process that is most reliably executed via a PC connection. The Android Open Source Project provides extensive documentation on the partition layout and boot process, which serves as the foundational knowledge for understanding why certain errors occur and how PC tools interact with the low-level software to rectify them.
The Strategic Advantage of PC-Based Repair Solutions
Repairing Android devices directly on the handset is often limited by the very errors being addressed. If the touchscreen is unresponsive or the display is black, on-device troubleshooting becomes impossible. PC-based tools bypass these limitations by establishing a direct communication channel with the device’s processor through USB protocols like Fastboot, Download Mode, or Emergency Download Mode (EDL). This external vantage point allows for the injection of clean system images, the wiping of corrupted cache partitions, and the relocking of bootloaders without needing the device’s UI to function. Furthermore, PC tools generally possess greater processing power and stability, reducing the risk of interruptions during critical write operations that could otherwise permanently damage the device.
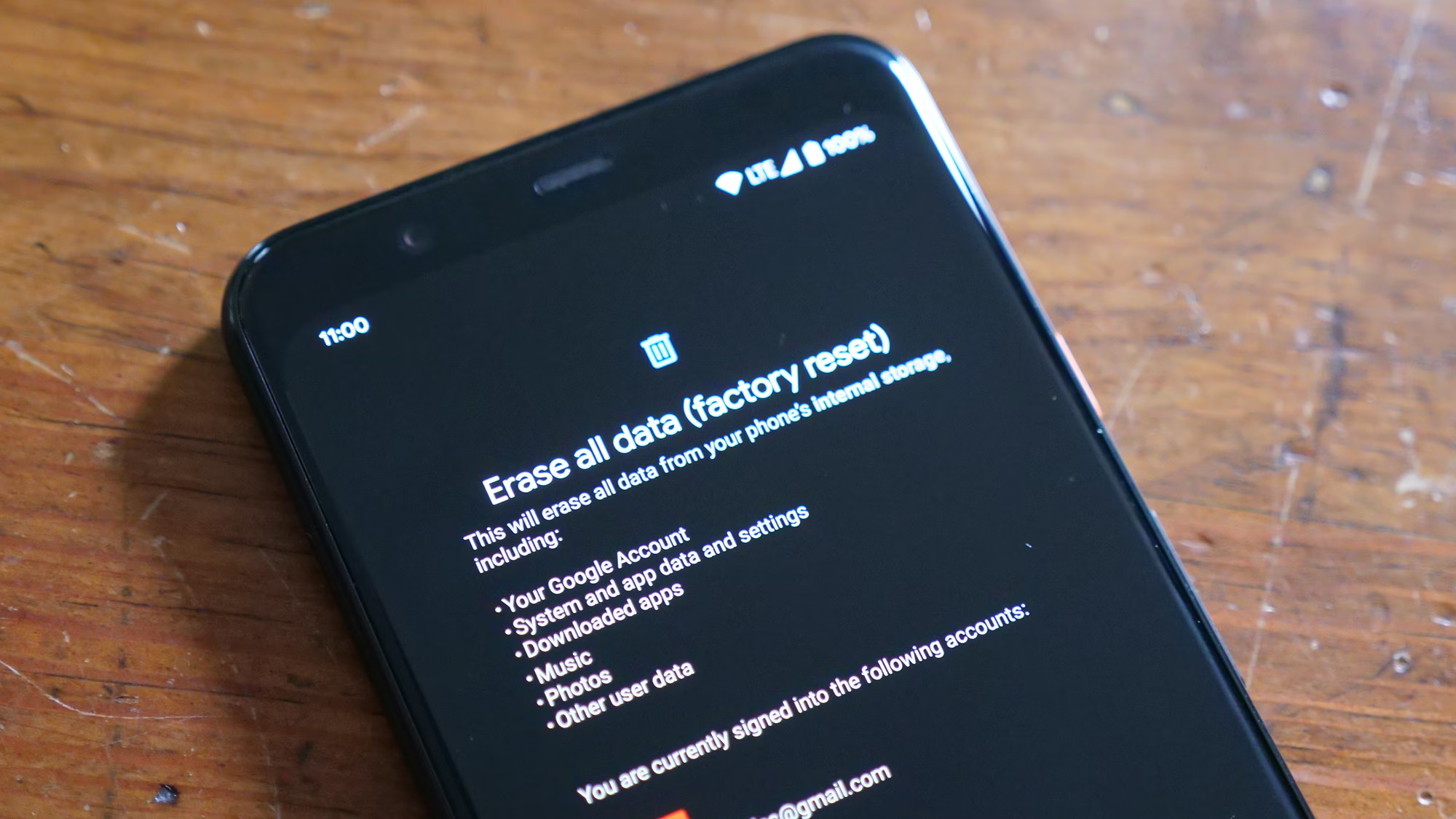
Professional repair environments rely on PC suites because they offer granular control over the flashing process. Tools can verify file integrity before writing to the flash memory, ensure proper driver handshake, and log every step of the operation for diagnostic purposes. This level of oversight is crucial when dealing with high-stakes repairs where data preservation is a priority. For instance, when addressing a boot loop caused by a failed update, a PC tool can force the device into a specific mode and flash only the affected partition, leaving user data untouched. In contrast, on-device factory resets often wipe everything indiscriminately. The Google Android Studio documentation outlines the protocols for device connectivity and debugging, highlighting the technical superiority of host-computer interventions for system-level repairs.
Essential Prerequisites: Drivers, Cables, and Environment
Before attempting any repair, establishing a stable physical and software connection between the PC and the Android device is paramount. The most common point of failure in DIY repairs is not the tool itself, but the environment in which it operates. High-quality USB cables are non-negotiable; cheap cables often lack the necessary shielding or wire gauge to sustain the consistent data throughput required for flashing firmware. A cable that works for charging may fail during a high-speed data transfer, causing the process to abort mid-write and potentially bricking the device. Similarly, USB ports on the computer matter. Direct connection to motherboard-backed USB 3.0 or higher ports is recommended over using unpowered hubs, which can introduce latency or power fluctuations.
On the software side, installing the correct USB drivers is the gateway to successful communication. Generic Windows drivers often fail to recognize devices in specialized modes like Fastboot or Download Mode. Manufacturers provide specific drivers that enable the PC to identify the hardware correctly. For Samsung devices, the Samsung USB Drivers are essential for Odin-based repairs. For Google Pixel and other AOSP-based devices, the Google USB Driver available through the SDK Manager is the standard. Failure to install these correctly results in the device appearing as an “Unknown Device” in the Device Manager, rendering repair tools useless. Additionally, disabling driver signature enforcement on Windows may be necessary for certain unsigned drivers used in legacy device repairs.
Navigating the Landscape of Professional Repair Tools
The market offers a variety of PC tools designed to repair Android system errors, each with its own strengths and specific use cases. Selecting the right tool depends heavily on the device manufacturer and the nature of the error. For Samsung devices, Odin is the industry standard. This lightweight utility allows users to flash official firmware files (typically in .tar or .md5 format) directly to the device’s partitions. Its interface is straightforward, mapping specific file types to their corresponding partitions (BL for bootloader, AP for system, CP for modem, and CSC for consumer software customization). The reliability of Odin has made it the go-to choice for technicians worldwide, supported by a vast repository of firmware available on sites like SamMobile, which hosts official images for nearly every Samsung model.
For devices utilizing the Qualcomm Snapdragon chipset, the QPST (Qualcomm Product Support Tools) suite and its companion QFIL (Qualcomm Flash Image Loader) are indispensable. These tools are particularly powerful for reviving hard-bricked devices that can only be detected in Emergency Download Mode (EDL). QFIL allows for the raw programming of the flash memory, effectively rebuilding the device’s software structure from the ground up. This method is often the last resort for devices that do not respond to standard Fastboot commands. Similarly, MediaTek-based devices rely on the SP Flash Tool (Smart Phone Flash Tool), which interacts with the BootROM to flash scatter-loading files. Understanding the chipset architecture is vital, as using a Qualcomm tool on a MediaTek device (or vice versa) will yield no results. Resources like the XDA Developers Forums serve as a critical hub for identifying the correct tools and firmware for specific hardware configurations.
Fastboot, a protocol included in the Android SDK Platform-Tools, represents the universal standard for AOSP-compliant devices. It allows for command-line interactions to unlock bootloaders, flash recovery images, and wipe partitions. While it lacks a graphical interface, its versatility makes it a fundamental skill for any technician. Commands such as fastboot flash recovery recovery.img or fastboot erase cache are routine procedures in system repair. The official Android Platform-Tools package ensures that users have the latest version of ADB and Fastboot, maintaining compatibility with newer Android versions and security patches. Mastery of these command-line tools provides a level of precision that graphical wrappers often obscure.
Step-by-Step Protocol for Safe Firmware Reflashing
The process of reflashing firmware to repair system errors follows a strict logical sequence to minimize risk. The first step involves sourcing the exact firmware match for the device’s model number and region code. Flashing firmware intended for a different region or variant can lead to IMEI loss, baseband errors, or permanent bricking. Once the correct files are downloaded and verified via checksum (MD5 or SHA256) to ensure integrity, the device must be powered off completely. Entering the specific download or fastboot mode usually requires a unique combination of hardware buttons, such as holding Volume Down and Power simultaneously. Connecting the device to the PC at this stage should trigger the installation of the specific drivers if not already present.
With the device in the correct mode and recognized by the PC, the chosen tool (e.g., Odin, QFIL, or Fastboot) is launched. In Odin, for example, the firmware components are loaded into their respective slots. It is crucial to verify that the “Auto Reboot” and “F. Reset Time” options are checked, while “Re-Partition” is left unchecked unless specifically instructed by a trusted guide, as incorrect partition files can destroy the device’s table of contents. Once the “Start” button is pressed, the tool begins the writing process. During this phase, the progress bar on the PC and the device screen indicates the status. Interrupting this process by disconnecting the cable or powering off the PC is catastrophic. Upon completion, the tool will display a “PASS” message, and the device will reboot. The initial boot may take several minutes as the system optimizes applications and rebuilds caches. Detailed guides on these procedures are often found on manufacturer-specific support pages or trusted technical repositories like GSM Forum, which cater to professional technicians.
Data Preservation Strategies During System Repairs
One of the primary concerns during system repair is the potential loss of user data. While some errors necessitate a full wipe, many can be resolved while preserving photos, messages, and applications. The key lies in the type of flash file used and the method of execution. In Samsung’s Odin tool, using the HOME_CSC file instead of the standard CSC file triggers an update process that retains user data, whereas the standard CSC performs a clean install. Similarly, in Fastboot, avoiding the fastboot -w command (which wipes userdata) is essential for data preservation. However, if the system partition is severely corrupted, retaining data may be impossible without first recovering it via specialized extraction methods.
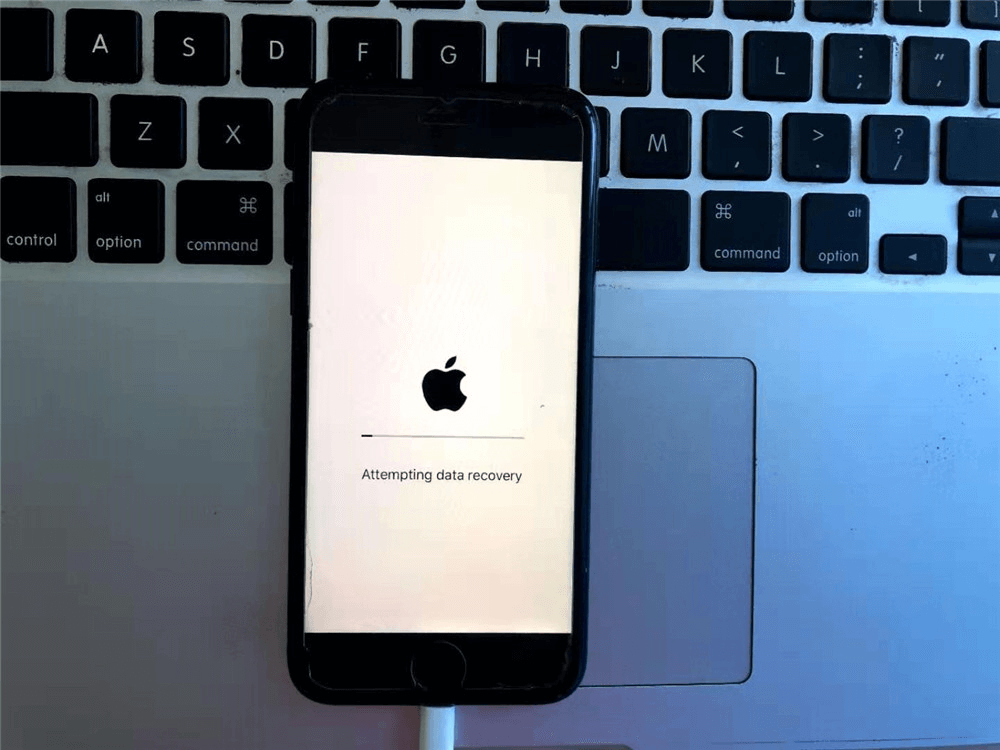
Before attempting any repair that carries a risk of data loss, creating a backup is the golden rule. If the device can still boot into recovery mode or has USB debugging enabled, tools like ADB can pull data from the internal storage to the PC. The command adb pull /sdcard/ C:/Backup/ can salvage critical files even if the OS is unstable. For devices that are completely unbootable, professional data recovery services may utilize chip-off techniques or JTAG interfaces, though these are beyond the scope of standard PC tool repairs. The National Institute of Standards and Technology (NIST) provides guidelines on mobile device forensics and data preservation, emphasizing the importance of write-blocking and verified copying procedures to maintain data integrity during troubleshooting.
Troubleshooting Common Post-Repair Issues
Even after a successful flash, devices may encounter post-repair anomalies. A common issue is the “Custom Binary Blocked by FRP Lock” error, which occurs when trying to flash unofficial or mismatched firmware on a device with Factory Reset Protection (FRP) active. Resolving this often requires flashing the exact original firmware version or unlocking the bootloader, a process that varies by manufacturer. Another frequent problem is the loss of network connectivity or IMEI nullification, typically caused by flashing incorrect modem (CP) files or corrupting the EFS partition. In such cases, restoring a previously backed-up EFS partition is the only viable solution, highlighting the importance of backing up device-specific calibration data before any major intervention.
Boot loops persisting after a flash usually indicate a cache conflict or a mismatched kernel. Wiping the cache and Dalvik cache from the custom recovery or stock recovery mode often resolves this. If the device gets stuck on the manufacturer’s logo, re-flashing the stock recovery image alongside the system image can restore the boot chain. In scenarios where the device enters a continuous reboot cycle immediately after the PC tool reports success, checking the battery voltage is advisable; low voltage can cause the processor to reset during the high-power demand of the boot sequence. Technical communities like Android Authority frequently publish troubleshooting flowcharts for these specific post-flash scenarios, offering community-verified solutions for complex edge cases.
Comparative Analysis of Leading Repair Tools
To assist in selecting the appropriate utility for specific repair scenarios, the following table compares the capabilities, compatibility, and risk profiles of the most prominent Android repair tools.
| Tool Name | Primary Compatibility | Interface Type | Data Preservation Capability | Best Use Case | Risk Level |
|---|---|---|---|---|---|
| Odin | Samsung Devices | Graphical (GUI) | High (with HOME_CSC) | Flashing official firmware, unbricking soft-bricked Samsung phones | Low |
| QFIL / QPST | Qualcomm Snapdragon | Graphical (GUI) | Low (Often requires full erase) | Reviving hard-bricked devices in EDL mode, raw programming | High |
| SP Flash Tool | MediaTek Devices | Graphical (GUI) | Moderate (Format All vs. Download Only) | Fixing boot loops, flashing stock ROM on MTK chips | Moderate |
| Fastboot | AOSP / Pixel / Generic | Command Line (CLI) | Variable (Depends on commands) | Unlocking bootloaders, flashing custom recoveries, partition management | Moderate |
| ADB (Android Debug Bridge) | All Android (USB Debugging On) | Command Line (CLI) | High (File pull/push) | Log analysis, app installation, sideloading updates, data backup | Very Low |
| Mi Flash Tool | Xiaomi Devices | Graphical (GUI) | Low (Clean All option wipes data) | Unbricking Xiaomi devices, switching between Global/CN ROMs | Moderate |
| LG UP | LG Devices | Graphical (GUI) | High (Upgrade mode) | Refurbishing LG phones, cross-flashing compatible firmware | Low |
| Hisuite | Huawei Devices | Graphical (GUI) | High (System repair mode) | Official firmware restoration for Huawei/Honor | Low |
This comparison underscores that no single tool is universal. The choice depends entirely on the hardware architecture and the specific state of the device. For instance, while Fastboot offers great flexibility, it requires command-line proficiency, whereas Odin provides a safer, guided experience for Samsung users. Understanding these distinctions prevents the misuse of tools that could exacerbate system errors.
Frequently Asked Questions
Can PC repair tools fix a hard-bricked Android phone?
Yes, PC tools like QFIL for Qualcomm devices or SP Flash Tool for MediaTek devices can often revive hard-bricked phones that show no signs of life. These tools communicate with the device’s BootROM in emergency modes (EDL or BROM), allowing the re-flashing of the primary bootloader and system partitions. However, success depends on the hardware being physically intact and the ability to force the device into the specific download mode.
Is it possible to repair system errors without losing data?
In many cases, yes. Tools like Odin (using the HOME_CSC file) or Fastboot (without the wipe flag) can repair the operating system while preserving user data. However, if the corruption affects the data partition itself or if the encryption keys are lost, data recovery may not be possible. It is always recommended to attempt a backup via ADB or cloud services before initiating any repair procedure.
What should I do if the PC does not recognize my Android device in Download Mode?
First, verify that the correct USB drivers are installed and that the Device Manager shows no unknown devices. Try switching to a different USB port, preferably a USB 2.0 port directly on the motherboard, and use a high-quality data cable. Sometimes, reinstalling the specific manufacturer drivers or disabling driver signature enforcement in Windows can resolve recognition issues.
Are there risks involved in unlocking the bootloader during repairs?
Yes. Unlocking the bootloader typically triggers an automatic factory reset, erasing all user data. Additionally, it may void the device warranty and disable certain security features like Widevine L1 (affecting HD streaming quality) or Samsung Knox. It also exposes the device to potential security vulnerabilities if not relocked properly after repairs.
How do I verify if the firmware file I downloaded is safe?
Always download firmware from reputable sources like the manufacturer’s official site, SamMobile, or trusted mirrors. Verify the file’s integrity by checking its MD5 or SHA256 hash against the value provided by the source. Mismatched hashes indicate a corrupted or tampered file that should not be flashed. Antivirus software can also scan the archive for malware before extraction.
What is the difference between Fastboot and Recovery Mode?
Fastboot is a protocol used to modify the flash filesystem via a USB connection from a PC, allowing for low-level partition writing. Recovery Mode is an independent runtime environment stored on a separate partition of the device, used for applying updates, wiping data, or performing factory resets without needing a PC. Both are essential for different stages of system repair.
Can flashing custom firmware cause permanent hardware damage?
Flashing incorrect firmware generally causes software-level damage (soft brick) rather than permanent hardware failure. However, repeatedly interrupting the flashing process or forcing incompatible voltage settings through modified kernels can theoretically stress the power management IC or flash memory. Sticking to official stock firmware minimizes these risks significantly.
Why does my device lose IMEI after flashing?
IMEI loss usually occurs when the EFS or Persist partition, which stores unique device identifiers and calibration data, is overwritten or corrupted. This happens when flashing firmware meant for a different region or model, or when using “Format All” options in flash tools. Restoring a backup of the EFS partition taken before the repair is the standard fix.
Conclusion
Repairing Android system errors using PC tools is a sophisticated process that bridges the gap between software glitches and hardware restoration. By leveraging the power of desktop-based utilities, users and technicians can diagnose deep-seated issues, reflash corrupted partitions, and revive devices that appear beyond repair. The journey from a boot-looping brick to a fully functional smartphone requires a disciplined approach: understanding the specific nature of the error, securing the correct drivers and firmware, selecting the appropriate tool for the device’s architecture, and executing the flash with precision. While the risks of data loss and further complications exist, adhering to established protocols and utilizing authoritative resources significantly mitigates these dangers.
The evolution of Android repair methodologies continues to advance, with tools becoming more robust and communities more knowledgeable. Whether utilizing Odin for a Samsung Galaxy, QFIL for a Snapdragon-powered flagship, or Fastboot for a Pixel device, the underlying principle remains the same: precise intervention restores order. As mobile devices become increasingly integral to personal and professional lives, the ability to safely navigate system repairs empowers users to extend the lifespan of their hardware and maintain digital continuity. With careful preparation and reliance on verified technical data, the daunting task of system repair transforms into a manageable, repeatable procedure, ensuring that technology serves its purpose without interruption.